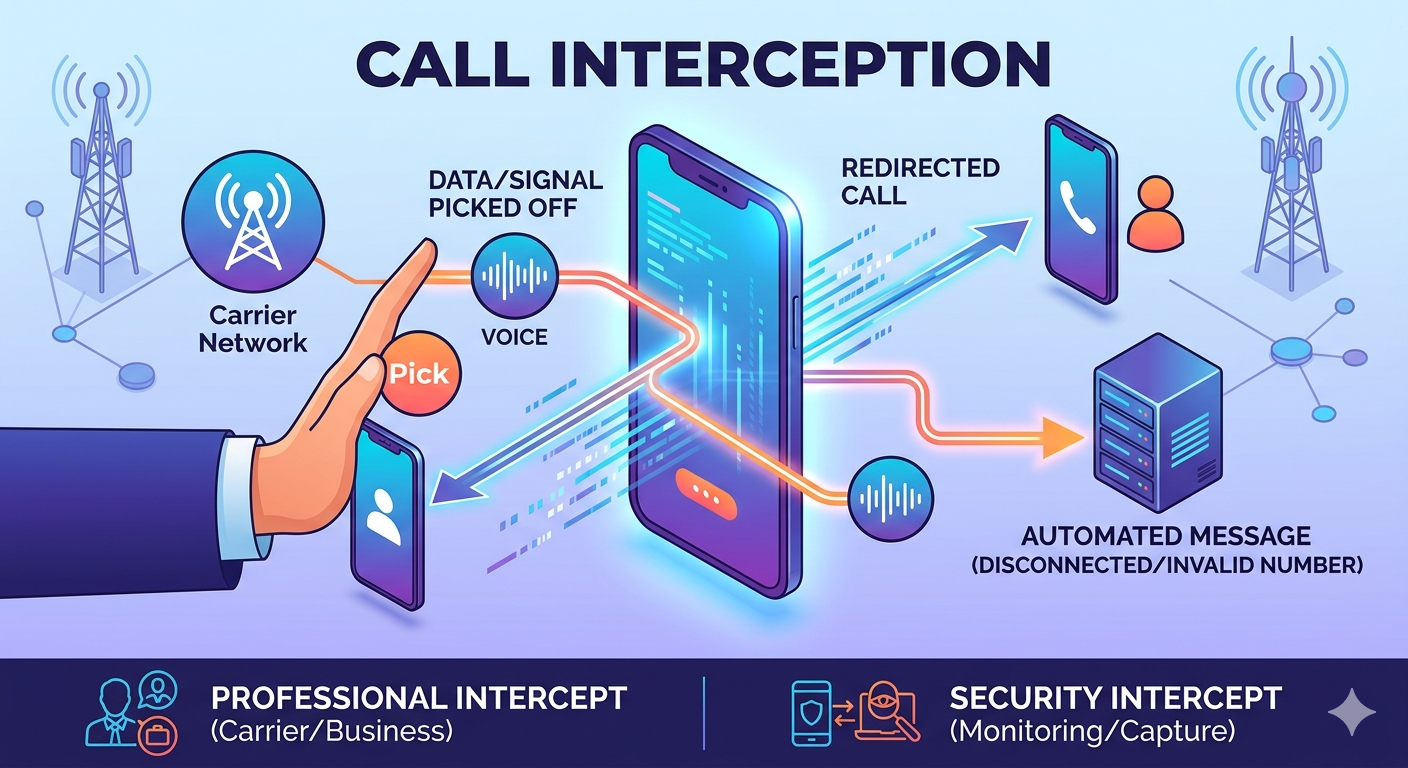
Call interception is a telecommunications process where a communication session is redirected, monitored, or terminated before it reaches the intended recipient. In a professional or carrier context, it refers to the automated management of calls that cannot be completed as dialed, often resulting in a recorded message explaining why the connection failed. From a security standpoint, it involves the unauthorized capturing of data or audio during a live conversation. Understanding the mechanisms behind these processes is essential for both businesses managing call flows and individuals looking to protect their private communications from external interference or surveillance.
What is Call Interception and How It Functions
In the world of modern telephony, call interception serves as a critical traffic management tool for service providers and enterprises. When a user dials a number, the network validates the destination; if the system identifies a reason the call cannot proceed, it triggers an intercept. This is not merely a failure to connect but a programmed response designed to provide the caller with specific information regarding the status of the line. The process involves a switching system that recognizes a trigger—such as an unassigned number or a busy signal—and routes the audio path to an announcement server rather than the target handset.
For businesses using advanced communication platforms, call intercepting functions as a way to filter unwanted traffic or manage high volumes of inbound inquiries. It allows administrators to set parameters that determine which calls are allowed to pass through to agents and which are handled by automated systems. This ensures that the network resources are utilized efficiently and that callers are not left in a state of perpetual ringing. By managing these touchpoints, organizations can maintain a high standard of professional interaction even when direct human connection is not immediately available or appropriate for the specific situation.
From a technical perspective, to intercept phone calls means to detach the signaling path from the physical device and re-route it. This is often seen in law enforcement scenarios where a legal warrant allows authorities to monitor a line, but it is also a fundamental part of how cellular towers handle handovers. When you move from one cell tower to another, the network must intercept the signal and transfer it seamlessly to maintain the conversation. While the term might sound invasive, the vast majority of daily instances involving an intercepted signal are routine automated tasks performed by global telecommunications infrastructure to ensure connectivity and order.
Why Do They Call an Interception a Pick
The terminology used in telecommunications often borrows from other industries or historical mechanical processes. The phrase why do they call an interception a pick is frequently discussed in the context of both sports and technical line management. In sports, specifically American football, a pick is synonymous with an interception because one player picks off a pass intended for another. In telephony, the term pick or picking up a line relates to the physical action of a switch or a relay grabbing a specific frequency or circuit. When a call is intercepted, the system picks the signal out of the standard routing path to place it elsewhere.
Another historical reason for this terminology involves the way manual switchboards functioned. Operators would physically pick a cord and plug it into a jack to complete or divert a call. If a call needed to be intercepted for administrative reasons, the operator would pick that specific line to provide an announcement. Over time, the slang transitioned into modern digital systems. Even though physical cords are no longer used, the concept of picking a call out of a queue to redirect it remains a core part of the jargon used by network engineers and support staff when discussing call intercept strategies and management.
In the contemporary sales and support environment, picking a call can also refer to the act of an experienced manager jumping into a live conversation to assist a junior representative. This is a form of intentional call intercept where the supervisor picks the active line to prevent a deal from falling through or to resolve a complex customer issue. Whether it is a carrier picking a signal to play a disconnected message or a manager picking a line to help a teammate, the underlying theme is the redirection of a communication flow from its original trajectory to a more controlled environment.

Common Types of Call Intercept in Telecommunications
There are several standard forms of interception that occur daily within global networks, most of which are designed to improve the user experience by providing clarity. One of the most frequent is the disconnected number intercept, which occurs when a caller attempts to reach a line that is no longer in service. Instead of silence or a generic error tone, the network provides a clear message stating the number is disconnected. This prevents the caller from repeatedly trying a dead line and helps maintain network efficiency by clearing the signaling path quickly.
Another common variety is the invalid number intercept, which triggers when a user dials a sequence of digits that does not correspond to any active phone format. This often happens due to typos or incorrect area codes. Similarly, blocked call intercepts are used by individuals or businesses to prevent specific numbers from reaching them. In these cases, the call is intercepted by a firewall or a carrier-level filter, and the caller may receive a message indicating that the person they are trying to reach is not accepting calls at this time. This is a primary tool for combating spam and harassment.
Network error and administrative intercepts are also vital for system health. If a specific part of the cellular grid is overloaded or experiencing a technical fault, the system will intercept cell phone calls and provide a fast busy signal or a recording asking the user to try again later. Administrative intercepts might be used during maintenance windows or when a subscriber has failed to pay their bill. In all these scenarios, the goal is to provide a structured response to a communication attempt that cannot be completed, ensuring that the caller is informed and the network remains organized.
How to Stop Call Interception and Enhance Security
For many users, the concern lies in unauthorized access to their conversations, leading to the question of how to stop call interception. To protect against malicious interception, the first step is to use encrypted communication channels. Traditional cellular calls are transmitted over radio waves which, while encrypted by carriers, can sometimes be vulnerable to sophisticated hardware like IMSI catchers. Utilizing Voice over Internet Protocol (VoIP) services that offer end-to-end encryption ensures that even if the data is captured, it cannot be decoded or listened to by outside parties.
Another effective way to manage and stop unwanted interception is to regularly check for call forwarding settings on your device. Hackers sometimes use MMI codes to redirect your calls to their own numbers without your knowledge. By dialing codes like *#21# or *#62#, you can see if your calls are being intercepted or forwarded to an unknown destination. If you find unauthorized forwarding, you can usually disable all redirections by dialing ##002#. Maintaining up-to-date software on your smartphone is also crucial, as manufacturers frequently release security patches that close vulnerabilities used by interception tools.
Physical security and network awareness are also important components of protecting your privacy. Avoid using public, unsecured Wi-Fi networks for sensitive conversations, as these are prime environments for man-in-the-middle attacks where a third party can intercept cell phone calls made via the internet. Using a reputable Virtual Private Network (VPN) can add an extra layer of security by masking your data traffic. For businesses, employing advanced threat detection systems that monitor for anomalies in call routing can prevent corporate espionage and ensure that sensitive internal communications remain private and secure from external intercepting attempts.
The Difference Between Call Intercept and Call Recording
It is important to distinguish between call intercepting and call recording, as they serve different purposes and are governed by different legal frameworks. Call recording is the process of capturing the audio of a conversation that has already been successfully connected between two or more parties. This is commonly used in customer service for quality assurance or in legal settings for documentation. Recording requires the call to be active and typically involves both parties being aware of the recording, depending on local “one-party” or “two-party” consent laws.
In contrast, call intercept happens before or during the connection phase and involves the redirection of the call itself. While an intercepted call can be recorded, the act of interception is more about the routing and control of the communication path. For example, a network operator might intercept a call to play a message, but they do not necessarily record the caller’s reaction. However, in a legal or law enforcement context, an intercept often leads to recording, as authorities use wiretaps to listen in on conversations in real-time to gather evidence.
From a business operational standpoint, a call intercept tool might be used to send a caller to a specific menu or an automated assistant, whereas a recording tool would only start functioning once the caller begins speaking to a live agent. Businesses must be careful to comply with the Electronic Communications Privacy Act (ECPA) in the United States, which provides the legal framework for when and how communications can be legally intercepted or recorded. Unauthorized interception is a serious federal offense, making it vital for companies to ensure their call management systems are configured within the bounds of the law.
Benefits of Using Call Intercept in Business
Implementing a professional call intercept strategy offers numerous advantages for organizations looking to streamline their communication. One of the primary benefits is that it prevents confusion for the customer. By providing a clear, recorded message when a line is busy or unavailable, the company manages expectations and provides professional closure to the call attempt. This is far superior to letting a phone ring indefinitely, which can frustrate customers and damage the brand’s reputation for reliability and accessibility.
Strategic interception also supports network efficiency and improves call flow control. By filtering out invalid numbers or known spam callers before they ever reach an agent, businesses can save significant time and resources. This ensures that live representatives are only dealing with legitimate inquiries, thereby increasing productivity. Furthermore, call intercepting can be used to route calls based on the time of day or the caller’s geographic location, ensuring that the person is always directed to the most appropriate department or the nearest office, which optimizes the overall customer journey.
-
Interception systems reduce the load on human operators by handling routine status messages automatically.
-
They provide a layer of security by filtering out malicious or fraudulent calls before they enter the internal network.
-
Businesses can use intercept data to analyze call patterns and identify common reasons why calls are failing.
-
Strategic redirects can turn a failed connection into a lead generation opportunity by offering alternative contact methods.
-
Maintaining a professional intercept message reinforces brand consistency across all points of communication.
Who Utilizes Call Intercept Systems
Telecommunications providers are the most prolific users of call intercept technology. They use it at a massive scale to manage the billions of calls that move through their switches every day. Without these systems, the phone network would be a chaotic environment filled with dead air and confusing signals. Carriers rely on interception to notify users about roaming charges, exhausted prepaid balances, or emergency network outages. It is the fundamental “language” the network uses to talk back to its users when a direct connection is not possible.
Customer support and sales teams also rely heavily on these tools to manage their inbound volume. For instance, a sales team might use a call intercept feature to ensure that high-priority clients are never met with a busy signal. Instead, the call is intercepted and rerouted to an available senior executive or a specialized VIP support line. This level of control allows businesses to prioritize their most valuable leads and ensure that no opportunity is lost due to a technical limitation or a lack of immediate staff availability.
IT and network administrators use interception for troubleshooting and security auditing. By monitoring how many calls are being intercepted and for what reasons, they can identify weak points in the infrastructure or detect potential attacks on the system. For example, a sudden spike in invalid number intercepts might indicate a “war dialing” attack where a hacker is trying to find active modem lines. By having a robust intercept system in place, administrators can quickly identify and block these threats, protecting the integrity of the corporate communication network.
Supporting Research and Facts on Call Interception
Research into telecommunications security highlights the importance of understanding how to stop call interception.
According to a report by the Federal Communications Commission (FCC), the implementation of the STIR/SHAKEN framework was a major step in authorized interception.
This technology allows carriers to intercept and flag calls with spoofed caller IDs, significantly reducing the success rate of phone-based scams. The FCC data shows that since the widespread adoption of these protocols, billions of fraudulent calls have been successfully intercepted before reaching consumers.
Furthermore, a study on cybersecurity trends by the Ponemon Institute indicates that unauthorized intercepting of mobile communications remains a top concern for global enterprises. The study found that nearly 30% of organizations surveyed had experienced some form of mobile-related data breach, which included the interception of sensitive voice calls. This underscores the necessity for end-to-end encryption and the regular monitoring of call routing paths. These facts demonstrate that while call interception is a vital tool for network management, it also represents a significant frontier in the ongoing battle for digital privacy and security.
Best Practices for Managing Intercepted Calls
When setting up a call intercept system, it is essential to provide clear and concise messages. Callers should immediately understand why their call was intercepted and what they should do next. Avoid using technical jargon; instead of saying “Error 404: Destination Unreachable,” use a friendly message such as “The number you have dialed is currently unavailable. Please check the number and try again.” This approach maintains a professional tone and reduces the likelihood of caller frustration.
Another best practice is to update intercept rules regularly. As businesses grow and change, old phone numbers might be reassigned or departments might be restructured. If the intercept rules are outdated, callers might be directed to the wrong information or an old recording. Monitoring intercept activity is also a key task for managers. By reviewing logs of intercepted calls, you can spot trends, such as a high volume of calls to a discontinued product line, which might indicate that your website or marketing materials still have the old contact information listed.
-
Use high-quality voice recordings for intercept messages to maintain a professional brand image.
-
Always offer an alternative, such as a website URL or an automated help menu, within the intercept message.
-
Test your intercept triggers regularly to ensure they are functioning as expected across different carriers.
-
Keep legal compliance at the forefront by ensuring all interception practices align with privacy regulations.
-
Integrate intercept data with your CRM to track which customers are having trouble reaching you.
Read More: Interactive Voice Response (IVR) Systems: optimizing Business Communication
Final Thought
Call interception is a sophisticated and multifaceted component of modern communication that balances network efficiency with user information. Whether it is a carrier explaining a disconnected line or a business rerouting a high-priority customer, the goal remains the same: to provide order and clarity in a complex digital landscape. By understanding what is call interception and how to stop call interception from unauthorized sources, individuals and businesses can better navigate the technical and security challenges of the modern age. Embracing these tools strategically while maintaining a vigilant eye on privacy ensures that every connection—or redirected attempt—serves a productive and secure purpose.
Frequently Asked Questions
-
What is the meaning of call interception?
The meaning of call interception refers to the process where a phone call is diverted from its original path to an automated message, a different recipient, or a monitoring system. In a professional context, it is a way for networks to handle calls that cannot be completed.
-
What is a call interceptor?
A call interceptor can refer to either a piece of software used by telecommunications companies to manage call routing or a hardware device used by security professionals (and sometimes malicious actors) to capture and listen to wireless signals.
-
What does *# 61 *# do?
Dialing *#61# is a diagnostic command used to check the status of your call forwarding when a call is not answered. It shows the number where your calls are being diverted, which is useful for identifying if your calls are being intercepted by an unauthorized party.
-
Can my phone calls be intercepted?
Yes, phone calls can be intercepted through various means, including carrier-side redirects, law enforcement wiretaps, or malicious hardware like Stingrays. Using encrypted messaging apps and checking your phone’s forwarding settings are the best ways to prevent unauthorized interception.
-
Is call interception the same as a wiretap?
While they are related, they are not identical. A wiretap is a specific type of legal interception used by law enforcement to record conversations. General call interception is a broader term that includes routine network management and automated carrier messages.